Static Application Security Testing (SAST) is a core component of secure software development for Java applications, particularly in enterprise and regulated environments. By analyzing source code without executing it, SAST helps identify security vulnerabilities early in the development lifecycle.
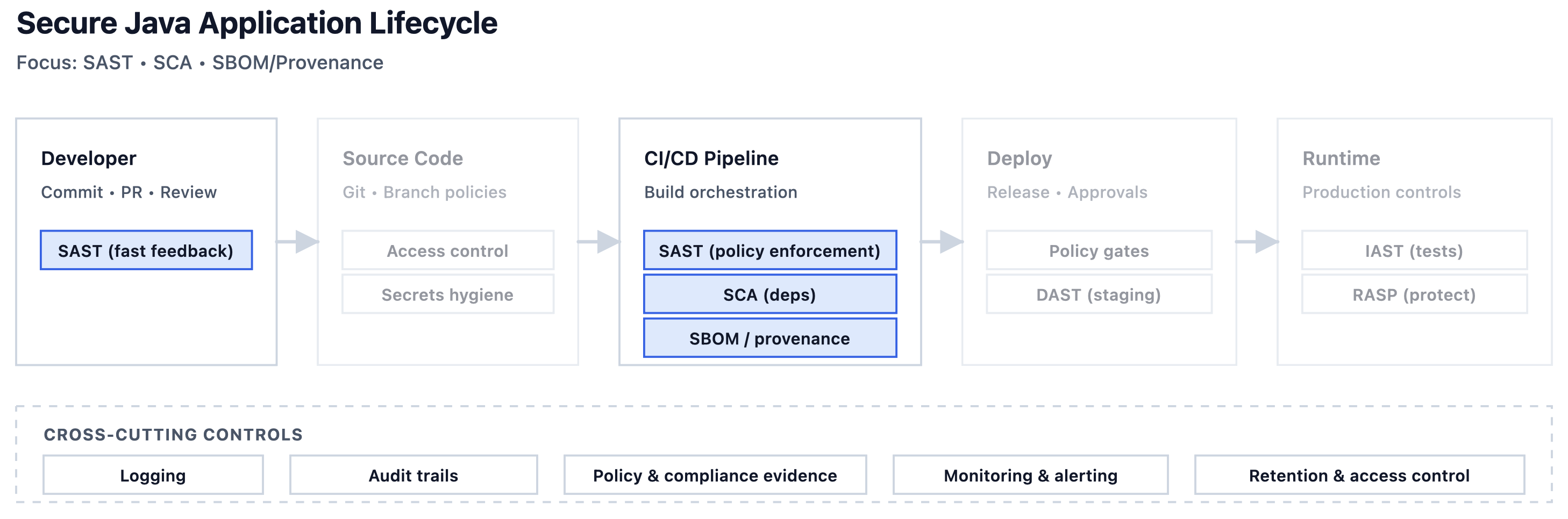
When integrated into CI/CD pipelines, SAST enables organizations to detect security issues automatically, reduce remediation costs, and improve overall software quality. This article explores how to effectively implement SAST for Java applications in CI/CD pipelines, with a focus on enterprise-scale and compliance-driven environments.
What Is SAST for Java Applications
SAST tools analyze Java source code, bytecode, or compiled artifacts to identify security vulnerabilities such as injection flaws, insecure cryptography usage, and improper authentication or authorization logic.
Unlike dynamic testing approaches, SAST operates early in the development process and does not require a running application. This makes it particularly suitable for automated CI/CD pipelines where fast feedback is essential.
Modern Java frameworks introduce abstractions that static analysis tools must understand, particularly when securing Spring Boot applications in enterprise environments.
Why SAST Is Critical in CI/CD Pipelines
CI/CD pipelines are the primary mechanism through which Java applications are built, tested, and deployed. Integrating SAST into these pipelines ensures that security checks are consistently applied to every code change.
In enterprise environments, SAST helps enforce secure coding standards, prevent vulnerable code from reaching production, and provide measurable security metrics. In regulated industries, SAST also contributes to compliance by demonstrating proactive vulnerability detection and remediation.
Common Java Security Issues Detected by SAST
SAST tools for Java typically detect a wide range of vulnerabilities, including:
- SQL injection and other injection flaws
- Cross-site scripting (XSS)
- Insecure deserialization
- Use of weak or broken cryptographic algorithms
- Hard-coded credentials
- Improper error handling and logging
These issues often map directly to well-known vulnerability categories such as the OWASP Top 10.
Integrating SAST into CI/CD Pipelines
SAST is commonly integrated into CI/CD pipelines as an automated build step. Scans are triggered on code commits, pull requests, or scheduled builds, depending on organizational policies.
In enterprise pipelines, it is important to balance scan depth with pipeline performance. Incremental scanning, pull request analysis, and asynchronous scans are often used to reduce feedback time while maintaining coverage.
Security gates can be configured to prevent builds from progressing when critical vulnerabilities are detected.
Performance and Scalability Considerations
One of the main challenges of SAST in CI/CD pipelines is performance. Large Java codebases can lead to long scan times, which may impact developer productivity.
To address this, organizations often tune SAST configurations, exclude non-critical code paths, and run full scans on a scheduled basis while using lighter scans for pull requests. Proper pipeline design is essential to ensure that security does not become a bottleneck.
SAST Results Management and Triage
SAST tools can generate a significant number of findings, including false positives. Effective triage processes are required to prioritize real risks and avoid alert fatigue.
In enterprise environments, SAST results are often integrated into issue tracking systems and security dashboards. Clear ownership and remediation workflows help ensure that findings are addressed consistently and efficiently.
SAST and Compliance Requirements
In regulated industries, organizations must demonstrate that security controls are in place to identify and manage vulnerabilities. SAST contributes to this by providing documented evidence of continuous security testing.
Audit trails, scan reports, and remediation records generated by SAST tools can support compliance with internal policies and external regulatory requirements. Proper configuration and documentation are essential to maximize this benefit.
In many organizations, SAST is formally defined as a mandatory control within CI/CD security policies and secure software delivery frameworks, which are commonly documented as part of an enterprise CI/CD security checklist.
Conclusion
SAST is a foundational security control for Java applications in CI/CD pipelines, particularly in enterprise and regulated environments. When properly integrated, it enables early detection of vulnerabilities, improves code quality, and supports compliance objectives.
By combining SAST with other CI/CD security practices and DevSecOps principles, organizations can significantly strengthen the security posture of their Java applications without compromising delivery speed.
